
How Often WHOIS Data Updates by TLD
Introduction WHOIS data update frequency exhibits significant variability across different top-level domains (TLDs) and registrars, posing non-trivial challenges...

WHOIS for New gTLDs: What Makes Them Different
Introduction WHOIS lookups for new generic top-level domains (new gTLDs) have diverged substantially from the uniform, predictable responses...

How ccTLD WHOIS Rules Differ From ICANN gTLDs
Introduction WHOIS data access and privacy controls exhibit significant variation across the domain landscape. While ICANN enforces a...
Building Autonomous AI Agents with Tool Use, Memory, and Planning
Introduction Autonomous AI agents demand more than reactive command execution—they must seamlessly integrate complex decision-making, dynamic external tool...
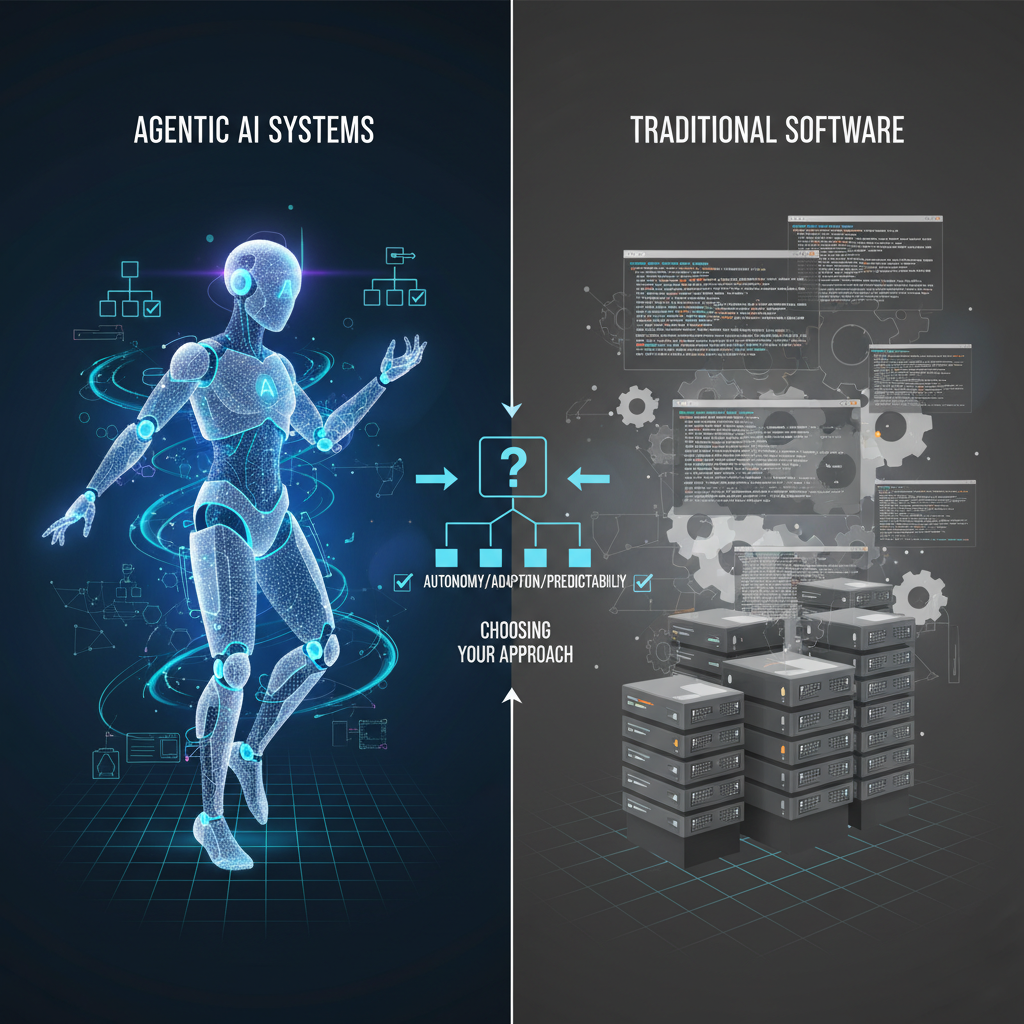
Agentic Systems vs Traditional Software: When and How to Use AI Agents
Introduction Traditional software architectures rely on deterministic, linear workflows that execute predefined tasks with limited adaptability. When deployed...

Context is the New API: Designing Context Pipelines for LLM Applications
Introduction Traditional API designs break down when interfacing with large language models (LLMs) because fixed endpoints cannot flexibly...

From Prompts to Context: Mastering AI Context Engineering for Reliable Systems
Introduction Large language models (LLMs) require far more than well-crafted prompts to deliver consistent, reliable outputs in production...

AI Agent Engineering in 2026: Architectures, Patterns, and Real-World Systems
Introduction AI agent engineering in 2026 confronts a multifaceted challenge: constructing distributed, multi-agent systems that maintain reliability and...

Beginner’s Guide to Domain Investing Using Data, Not Guesswork
Introduction Domain investing is frequently characterized as an exercise in intuition and luck. However, relying solely on guesswork...

What Is WHOIS History and Why It Matters
Introduction Tracking the full timeline of domain registration data is deceptively complex. WHOIS history captures not just the...

How to Track WHOIS Changes Over Time Automatically
Introduction Tracking WHOIS changes over time is rarely straightforward in production environments. Variations in data formats across registrars,...

How to Track Domain Ownership Changes Over Time
Introduction Domain ownership changes rarely manifest as clean, instantaneous events. Between ICANN’s mandatory 60-day transfer locks, inconsistent WHOIS...

WHOIS vs Marketplaces: Which Is Better for Domain Research?
Introduction Domain research tools underpin systems responsible for domain management, cybersecurity monitoring, and digital asset investment. Their effectiveness...

Expired Domains Explained: How to Find and Evaluate Them
Introduction Expired domains occupy a uniquely dynamic phase in the domain lifecycle where ownership and access rights transition...

How to Find the Real Owner of a Domain (Legally)
Introduction Modern domain ownership lookup is no longer a straightforward WHOIS query. Since the enforcement of GDPR obscured...

WHOIS History: Why Past Ownership Can Make or Break a Deal
Introduction Domain ownership is far more than merely representing the registrar holding a domain today. It is a...

Domain Age Explained: Why It Matters for SEO and Value
Introduction Domain age may seem like a straightforward metric—simply a timestamp extracted from WHOIS records—but its accuracy and...

How Domain Investors Use WHOIS Data to Find Deals
Introduction WHOIS data forms the foundational backbone of domain investing, yet its practical utility is hampered by inconsistent...

WHOIS Red Flags to Watch for When Buying Domains
Introduction Domains rarely fail silently—issues in ownership or configuration often ripple through DNS resolution, SSL validation, and security...

How to Research a Domain Before Buying It
Introduction Acquiring a domain without thorough vetting is an operational risk that can silently undermine system stability, security...